
Introduction
Telehealth has permanently reshaped healthcare delivery. FAIR Health reports that national telehealth utilization steadily increased from July to December 2024, underscoring that remote care is no longer an emergency workaround—it's infrastructure.
The risk that comes with it is just as significant: IBM Security found that healthcare data breaches cost an average of $9.77 million in 2024, the highest of any industry for the 14th consecutive year.
The same digital platforms enabling remote consultations, prescription workflows, and patient monitoring also expose protected health information (PHI) across devices, cloud vendors, third-party integrations, and state lines. Each connection point is a potential compliance gap.
Navigating that exposure requires more than good intentions. This guide covers the regulatory framework healthtech companies must comply with, the technical safeguards that matter most, vendor due diligence obligations, and how to staff the internal team to own compliance from policy to practice.
TLDR
- COVID-era HIPAA enforcement flexibilities ended in August 2023; full Privacy Rule, Security Rule, and Breach Notification Rule compliance is now mandatory for telehealth platforms
- End-to-end encryption, multi-factor authentication, role-based access controls, and audit logging are non-negotiable technical safeguards for HIPAA-compliant telehealth environments
- Every third-party vendor accessing patient data must sign a Business Associate Agreement (BAA); refusal signals direct compliance risk
- State privacy laws frequently exceed HIPAA and vary widely, making cross-state telehealth delivery a significant regulatory challenge
- HealthTech companies need compliance and security professionals who understand both HIPAA requirements and digital health infrastructure
What Is Telehealth Security Compliance?
Telehealth security compliance is the set of regulatory obligations, technical controls, and organizational policies a healthtech company must maintain to lawfully deliver remote care services and protect patient health information. It's distinct from general data security compliance because it specifically governs the handling of protected health information (PHI) in a healthcare context.
Who it applies to:
- Healthcare providers who use telehealth platforms for patient consultations (HIPAA-covered entities)
- Telehealth platform vendors, EHR integrators, communication software providers, AI transcription services, and cloud storage providers (business associates)
Being a HealthTech company rather than a direct care provider does not exempt you from these obligations. If your platform creates, receives, maintains, or transmits electronic PHI (ePHI) on behalf of a covered entity, you are a business associate under HIPAA — and the full ruleset applies.
That scope is broader than many early-stage healthtech teams expect, which is part of why the compliance environment has tightened significantly over the past two years.
The End of COVID-Era Enforcement Flexibility
During the COVID-19 public health emergency, HHS introduced temporary enforcement discretion allowing non-HIPAA-compliant platforms — including Apple FaceTime, Facebook Messenger video, Google Hangouts, Zoom, and Skype — to be used for telehealth in good faith. That flexibility expired on May 11, 2023, with a 90-day transition period ending August 9, 2023.
Any platform still relying on those carve-outs after August 2023 is operating out of compliance. Full HIPAA requirements now apply across the board, with no exceptions for the tools used during the pandemic.
The Regulatory Framework: HIPAA and Beyond
The Three Core HIPAA Rules
HIPAA compliance for telehealth centers on three regulations:
Privacy Rule: Governs all uses and disclosures of PHI. It defines permissible uses, patient rights, and what constitutes an authorized disclosure.
Security Rule: Governs electronic PHI (ePHI) specifically, requiring administrative, physical, and technical safeguards. Because virtually all telehealth involves electronic transmission, this rule is central to remote care compliance.
Breach Notification Rule: Governs how and when organizations must report unauthorized disclosures of PHI. Covered entities must notify affected individuals, HHS, and in some cases the media when breaches affect 500+ individuals.
Security Rule Safeguard Categories
The Security Rule requires three types of safeguards:
- Administrative safeguards: Security policies, workforce training, risk assessments, and incident response procedures
- Physical safeguards: Device controls, facility access restrictions, and workstation security
- Technical safeguards: Encryption, access controls, audit logging, and authentication mechanisms

The Audio-Only Exception
HHS OCR clarifies that the HIPAA Security Rule does not apply to audio-only telehealth provided over a standard telephone landline (PSTN) because the information transmitted is not electronic. However, VoIP, mobile apps, and internet-connected platforms are fully covered and must comply with all Security Rule requirements.
State Law Preemption
State regulations can preempt HIPAA when they offer stronger patient protections. Examples of stricter state requirements:
- Breach notification timelines: Florida, Washington, and Colorado require notification within 30 days; California mandates 15 business days for certain facilities—well under HIPAA's 60-day outer limit
- Cross-state licensing: Most states require clinicians to be licensed where the patient is physically located during the telehealth visit, not where the provider is located
- Broader covered entity definitions: Some states expand who qualifies as a covered entity beyond HIPAA's federal standard
Consult current state statutes or attorney general guidance — requirements change frequently.
Additional Regulatory Layers
Beyond HIPAA, healthtech companies may encounter three additional compliance frameworks depending on the services they offer:
DEA requirements for remote prescribing: The DEA issued a Fourth Temporary Extension of COVID-19 telemedicine flexibilities through December 31, 2026, allowing DEA-registered practitioners to prescribe Schedule II-V controlled substances via audio-video telemedicine, and certain Schedule III-V narcotics for opioid use disorder via audio-only telemedicine when other conditions are met.
42 CFR Part 2 for substance use disorder records: HHS/SAMHSA updated 42 CFR Part 2 to align more closely with HIPAA, effective April 16, 2024, with a compliance date of February 16, 2026. It permits a single patient consent for treatment, payment, and operations disclosures and applies HIPAA civil and criminal penalties for Part 2 violations.
CMS telehealth reimbursement rules: Through December 31, 2027, Medicare beneficiaries can receive telehealth services anywhere in the U.S.; beginning January 1, 2028, most pre-pandemic geographic and originating site limits return except for behavioral health.
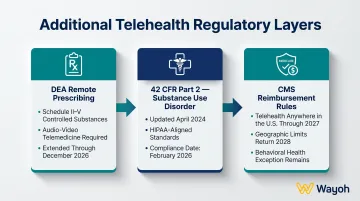
Each of these frameworks can introduce its own documentation, credentialing, and operational requirements — which is why telehealth platforms increasingly hire dedicated compliance staff before they scale, not after.
Essential Technical Safeguards for Telehealth Platforms
End-to-End Encryption
All data in transit and at rest must be encrypted. This includes:
- Video and audio streams during live consultations
- Messaging and chat transcripts
- Stored recordings and session notes
- Patient documents and images
Platform selection implications: Solutions that cannot guarantee encryption of stored content or that record sessions on unencrypted third-party servers introduce unacceptable risk. Healthcare-native platforms typically build encryption by default; general-purpose communication tools often do not.
Multi-Factor Authentication (MFA)
MFA is mandatory for any system where clinical staff access ePHI. Username and password alone are insufficient given the volume of credential-based attacks targeting healthcare.
Verizon's 2024 Data Breach Investigations Report found that credentials were involved in 13% of confirmed healthcare breaches. Multi-factor authentication substantially reduces this risk by requiring a second verification factor—such as a mobile authenticator app, SMS code, or hardware token—beyond the password.
Role-Based Access Controls and Least Privilege
Clinical staff, administrative users, and patients should each have differentiated access credentials that limit PHI visibility to what is minimally necessary for their function.
Telehealth platforms must support configurable permission tiers:
- Clinicians: Access to patient records, consultation history, and prescribing tools
- Administrative staff: Access to scheduling, billing, and contact information—not clinical notes
- Patients: Access to their own records, appointment history, and messages with their care team
This principle of least privilege reduces exposure if credentials are compromised.
Audit Logging
The HIPAA Security Rule requires that access to ePHI be trackable on a per-user basis. Telehealth platforms must generate, store, and make accessible logs that capture:
- Who accessed which records
- When the access occurred
- What actions were taken (view, edit, download, share)
Audit logs serve two purposes: compliance verification and breach detection. When a security incident occurs, these trails allow organizations to determine exactly what data was exposed and who was affected.
Automatic Session Controls
Session management controls are among the simplest safeguards to implement—and among the most frequently skipped:
- Automatic log-off after inactivity: Prevents unauthorized access if a device is left unattended
- Remote session termination: Allows IT teams to end active sessions if a device is lost or stolen
- Sign-out protocols at visit conclusion: Ensures patient data is not left visible on shared screens

Together, these controls close a gap that technical encryption alone cannot address: human behavior in clinical environments.
Vendor and Business Associate Due Diligence
The Business Associate Agreement Requirement
Under HIPAA, any third party that creates, receives, maintains, or transmits ePHI on behalf of a covered entity is a business associate and must sign a Business Associate Agreement (BAA) before any ePHI can be shared.
This applies to:
- Telehealth platform vendors
- Cloud storage providers
- EHR systems
- AI transcription services
- Scheduling tools
- Payment processors handling patient billing data
Vendors who refuse to sign a BAA—even large, reputable providers like Zoom or Google in their consumer forms—cannot be lawfully used for telehealth involving ePHI. HHS guidance on cloud computing clarifies that even if a cloud service provider only stores encrypted ePHI without the decryption key, a HIPAA-compliant BAA is still required.
The enterprise vs. consumer distinction matters here:
- Zoom offers HIPAA BAAs for paid plans with specific compliance features enabled; the free consumer product is not sufficient
- Google Workspace (paid) provides HIPAA BAAs; consumer Google Meet and Gmail do not
Key Vendor Evaluation Questions
Before selecting a telehealth platform or service provider, ask:
- Does the vendor sign a BAA?
- Is the connection end-to-end encrypted regardless of medium (video, audio, messaging)?
- Does the platform support role-based access and audit logging?
- Was the platform purpose-built for healthcare, or is it a general-purpose tool being adapted?
- Where is data stored, and does the vendor subcontract to other processors?
Healthcare-native platforms are far more likely to have these controls built in by default. That said, most telehealth organizations don't run on a single platform—they run on several.
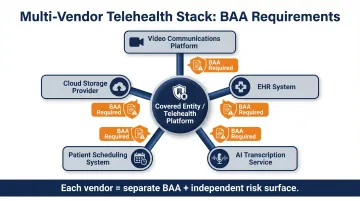
Multi-Vendor Environment Complexity
Modern telehealth stacks often layer multiple components:
- A video communications platform
- An EHR system
- An AI-assisted transcription service
- A patient scheduling system
- A cloud storage provider
Each component is a separate business associate requiring its own BAA. Each also represents a distinct risk surface that should be included in the organization's annual HIPAA risk assessment.
Ongoing Vendor Monitoring Obligations
A covered entity can be held liable for a business associate's HIPAA violation if it knew—or should have known through reasonable diligence—that the associate had a pattern of non-compliant behavior.
In 2016, HHS reached a $1.55 million settlement with North Memorial Health Care after the organization disclosed PHI to Accretive Health without a BAA and failed to conduct a risk analysis. The absence of a BAA and lack of oversight contributed directly to the penalty.
Organizations must conduct periodic reviews of business associate compliance—not just sign agreements and move on.
Operational Best Practices for Telehealth Compliance
Annual HIPAA Risk Assessment
The annual HIPAA risk assessment anchors every telehealth compliance program. It must extend to cover telehealth-specific risks:
- The platforms used for consultations, messaging, and document sharing
- The vendors involved and their security postures
- Data flows across the telehealth environment
- Device security (clinician workstations, mobile devices, patient endpoints)
HHS provides a Security Risk Assessment Tool developed by ONC in collaboration with OCR to assist small and medium-sized healthcare organizations and business associates in assessing Security Rule compliance.
Workforce Training Specific to Telehealth
Clinicians and staff must understand compliant session conduct and security protocols:
- Physical environment: Conduct consultations in private locations, use headsets to prevent audio spillage, position screens to prevent unauthorized viewing
- Phishing awareness: Recognize phishing attempts targeting telehealth logins
- Sign-out protocols: Always log out and close sessions at the end of consultations
- Breach response: Know what to do if a suspected breach occurs
Gaps in any of these areas can constitute a HIPAA violation — and enforcement history bears that out. HHS settled with Yakima Valley Memorial Hospital for $240,000 after security guards repeatedly accessed patient records without authorization, a case that illustrates exactly what inadequate training controls cost in practice.
Patient Identity Verification and Consent
Covered entities must have documented procedures for verifying patient identity at first contact and when credentials may have been compromised. HHS guidance states that the HIPAA Rules do not mandate a specific method to verify identity, but covered entities should be mindful of civil rights and other applicable laws.
On the consent side, organizations should obtain recorded consent when a consultation cannot be guaranteed confidential — for example, when a patient is in a public location or a third party is present during the session. This protects both the patient and the provider in the event of inadvertent disclosure.
Building the Right Compliance Team for HealthTech
Why Technology Alone Isn't Enough
Compliance cannot be sustained by platforms and policies alone. HealthTech companies need dedicated human expertise to own the compliance function:
- Privacy Officer: Responsible for HIPAA policy management, patient rights, and disclosure tracking
- Security Officer: Oversees technical safeguard implementation, incident response, and vulnerability management
- Regulatory Affairs Professionals: Track state-level telehealth law changes, CMS policy updates, and DEA prescribing requirements

As the platform scales, these roles become full-time positions, often supported by legal counsel and external advisors.
The HealthTech Hiring Challenge
Compliance professionals who understand HIPAA and healthcare data privacy are in demand. Finding candidates who also grasp the technical realities of digital health platforms—APIs, cloud infrastructure, AI integrations, and third-party data flows—is a different challenge entirely.
That intersection is where the talent gap shows up most. The median annual wage for compliance officers was $78,420 in May 2024, but candidates who combine healthcare regulatory expertise with hands-on digital health experience command significantly higher compensation — and they don't stay on the market long.
For many early-stage and growth-stage telehealth companies, this is the first compliance hire — and a wrong fit can set a regulatory program back by months. Wayoh works with HealthTech companies on exactly this problem, placing compliance, privacy, and regulatory affairs professionals from the founding hire through full team build-out. In a sector where the right candidate is rarely visible through a job posting, that search capability matters.
Frequently Asked Questions
What is telehealth compliance?
Telehealth compliance refers to the regulatory, technical, and operational requirements a healthcare organization or healthtech company must meet when delivering or supporting remote care services. This centers on HIPAA's Privacy Rule, Security Rule, and Breach Notification Rule, alongside applicable state laws.
What is required for HIPAA-compliant telehealth?
HIPAA-compliant telehealth requires conducting regular risk assessments, implementing administrative, physical, and technical safeguards for ePHI, executing BAAs with all vendors who access patient data, maintaining audit logs, and training staff on compliant telehealth conduct.
Do Business Associate Agreements apply to telehealth platforms?
Yes. Any vendor whose platform stores, transmits, or processes ePHI—including video platforms, cloud providers, EHR systems, and AI tools—qualifies as a business associate under HIPAA and must sign a BAA before being used for telehealth involving patient data.
What technical safeguards are required for telehealth security?
Required technical safeguards include:
- End-to-end encryption for data in transit and at rest
- Multi-factor authentication
- Role-based access controls enforcing least privilege
- Audit logging with per-user ePHI access tracking
- Automatic session log-off capabilities
How do state laws affect telehealth compliance?
State laws can be more restrictive than HIPAA and may preempt federal rules. States differ in breach notification windows, definitions of covered entities, cross-state licensing requirements, and specific restrictions on telehealth services, requiring healthtech companies to assess requirements in every state where they operate.
What happens if a telehealth platform violates HIPAA?
Penalties range from corrective action plans and civil monetary fines (tiered by the nature and willfulness of the violation) to criminal referral for knowing disclosures of ePHI. Covered entities can also face liability for associate violations if they failed to exercise reasonable oversight.


